Reward your researchers fairly – try our bug bounty calculator today!
Telecommunications
Stronger networks, safer connections
Complex, interconnected systems are the norm for telecommunication companies, and the risk of cyber threats is constant. Intigriti helps proactively identify and address vulnerabilities by connecting you with a global community of 150,000+ ethical hackers, bringing expert insight and real-world testing to your security strategy.
Advanced security testing for telecom companies
Telecom networks are increasingly interconnected and continuously evolving, introducing new technologies and services rapidly. This complexity can create opportunities for cybercriminals to exploit vulnerabilities and cause broad disruptions. Regular, rigorous security testing helps identify and address these risks early.
Maximize ROSI
With a community of researchers and triage team, you only pay for valid findings.
Security posture
While complying with industry regulations such as IMO, GDPR, TAS, EPA, C-TPAT, and many more.
Reduce disruptions
Avoid substantial costs incurred during disruptions from security breaches.
Continuous testing
Proactively address and mitigate vulnerabilities with continuous security testing.
Our clients in telecommunications
What’s safe today may not be safe tomorrow, but at least we are trying to do our best, and we show to our customers that we absolutely do our best to keep the platform safe.
Sándor Incze
CISOIntigriti’s platform
Protect your brand and build consumer trust by proactively safeguarding against vulnerabilities and preventing cyberattacks before they happen. Our industry-leading bug bounty platform connects you with 150,000+ ethical hackers worldwide, ensuring robust protection and optimizing ROSI on cybersecurity.
Overcoming today’s security challenges
Real world testing
Telecom is a high-value target for both cybercriminals and state-sponsored actors. Receive ongoing, real-world testing that adapts to new threats faster than traditional security assessments.
Monitor emerging tech
New technologies introduce unfamiliar attack vectors that traditional testing may miss. Bring diverse expertise to uncover vulnerabilities early in the development and deployment process.
Secure infrastructure
Your networks span countless endpoints and systems, making it difficult to monitor all potential vulnerabilities. Leverage a global community to test across this vast attack surface.
Protecting customer data
Your team handles vast amounts of sensitive user data. Continuous testing through bug bounty helps identify potential exposure risks before they’re exploited.
Securing legacy systems
Old infrastructure often lingers within telecom environments, creating blind spots and compatibility issues. Identify weaknesses that are often overlooked by automated tools or internal teams.
Supply chain fortified
Reliance on third-party vendors increases exposure to inherited vulnerabilities. Scope to test integrations and components, helping identify security risks introduced externally.
Testing tailored to you
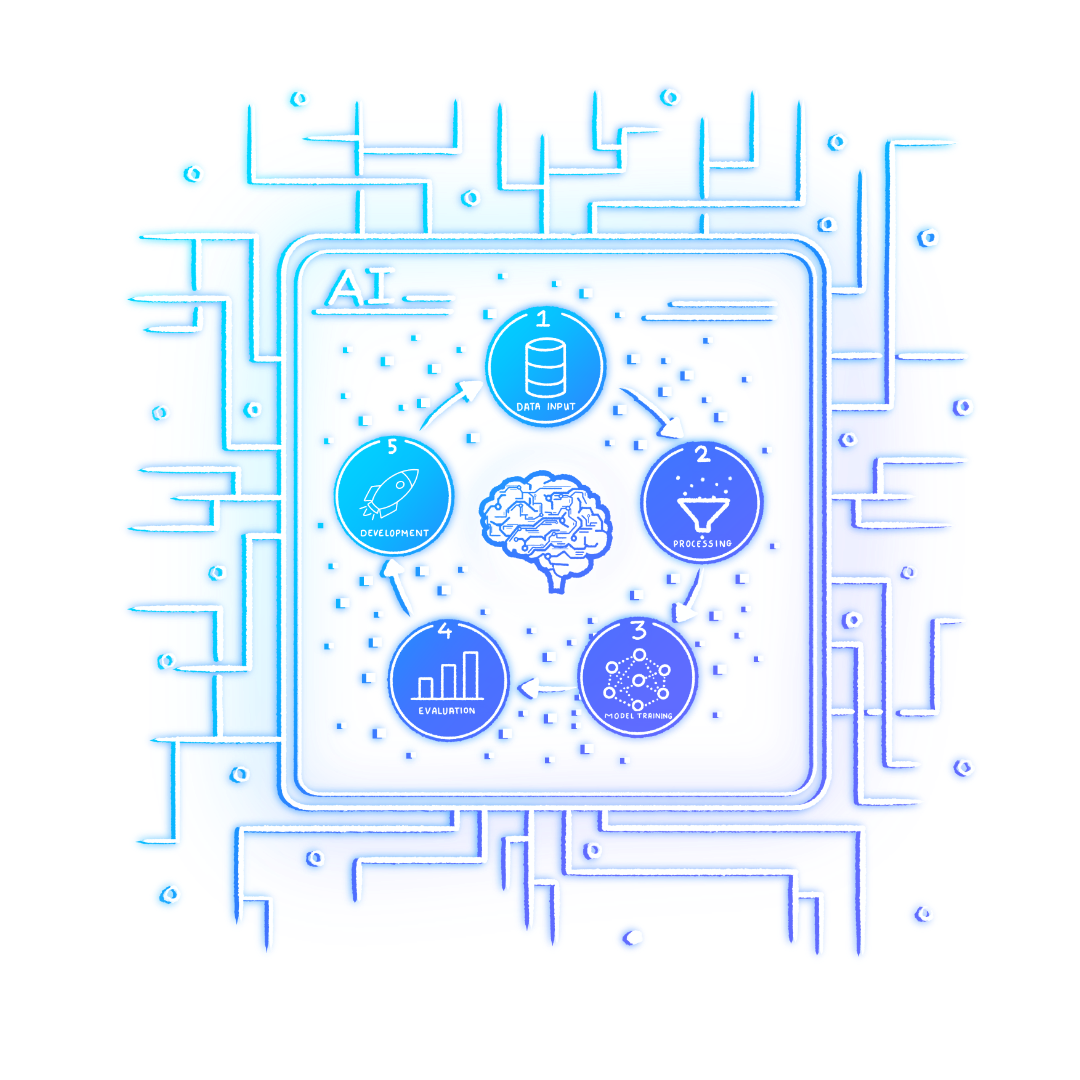
Be it bug bounty, VDP, PTaaS, or a combination of all, our innovative crowdsourced approach provides the Telecommunication industry with the processes to fortify digital assets and secure business using a vast community of cybersecurity professionals.
Bug bounty
Secure your assets using our expert community of ethical hackers. Intigriti’s bug bounty services allow you to secure your business using our huge community of cybersecurity professionals.
PTaaS
Pentest as a Service
PTaaS programs for test assurance & compliancy in a pay for value & time boxed program
VDP
Get ahead with Intigriti's Vulnerability Disclosure Program
Live hacking events
Generate buzz while finding bugs in a unique setting.
An introduction to crowdsourced cybersecurity for businesses
Tap into ethical hacking communities to stay ahead of emerging cyber threats and bolster your security posture.
Continue learning
CM.com
Discover how CM.com has integrated its managed bug bounty program into its security testing program. The global leader in cloud software has not only increased customer trust and its overall cybersecurity posture, but also improved internal skills and knowledge.
Six common bug bounty myths
When it comes to bug bounty programs, many misconceptions still linger on. Download our free eBook to get a better handle on bug bounty programs so that, moving forward, you can confidently separate the truths from the myths.
Money talks: optimize your security testing budget
Discover the secret to evolving your security testing through a bug bounty program, without blowing your budget.