Reward your researchers fairly – try our bug bounty calculator today!
Join our crowd
of ethical hackers.
Hack. Earn. Repeat.
400+
150K+
€50M+
Brands partnering with ethical hackers to stay secure
Are you a company?
Intigriti specializes in crowdsourced cybersecurity services that help organizations protect themselves from cybercrime and data breaches.
Our platform
Easy to use, streamlined platform that is continuously evolving to meet our researchers' needs.
Earn bug bounty rewards
Companies will reward you for alerting them to exploitable security bugs in their digital assets. Simply track down and submit unique, in-scope vulnerabilities, and we’ll do the rest.
Easy communication
No more switching between multiple communication tools. By interacting with companies and our triage team directly through the platform, you can stay focused on the task at hand.
Connect with your peers
Get inspired by the work of others and embrace the opportunity to collaborate. Before you know it, you could earn a top spot on our leaderboard.
Do what you love
We work with organizations of all sizes and across various industries. You decide what programs you want to be part of and how much time you dedicate to them.
Develop your skills
Intigriti offers a wide variety of bug bounty programs across several industries. Our platform connects you with programs that match your ambitions and skillset, and our expert triage team works with you to maximize your success.
The latest hacker news
Based in the Netherlands, Stefan Goossens, otherwise known as G0053, is both an independent security researcher and a partner for a marketing and web development company. As someone who loves nothing more than building and breaking web applications, Stefan is perfectly placed at the intersection of
Security teams running Bug Bounty programs often require similar insights and reporting to prove the value and ROSI for security initiatives, and often ask questions such as: What changed? Where are we spending? Are we improving? What needs attention right now? Until now, answering thos
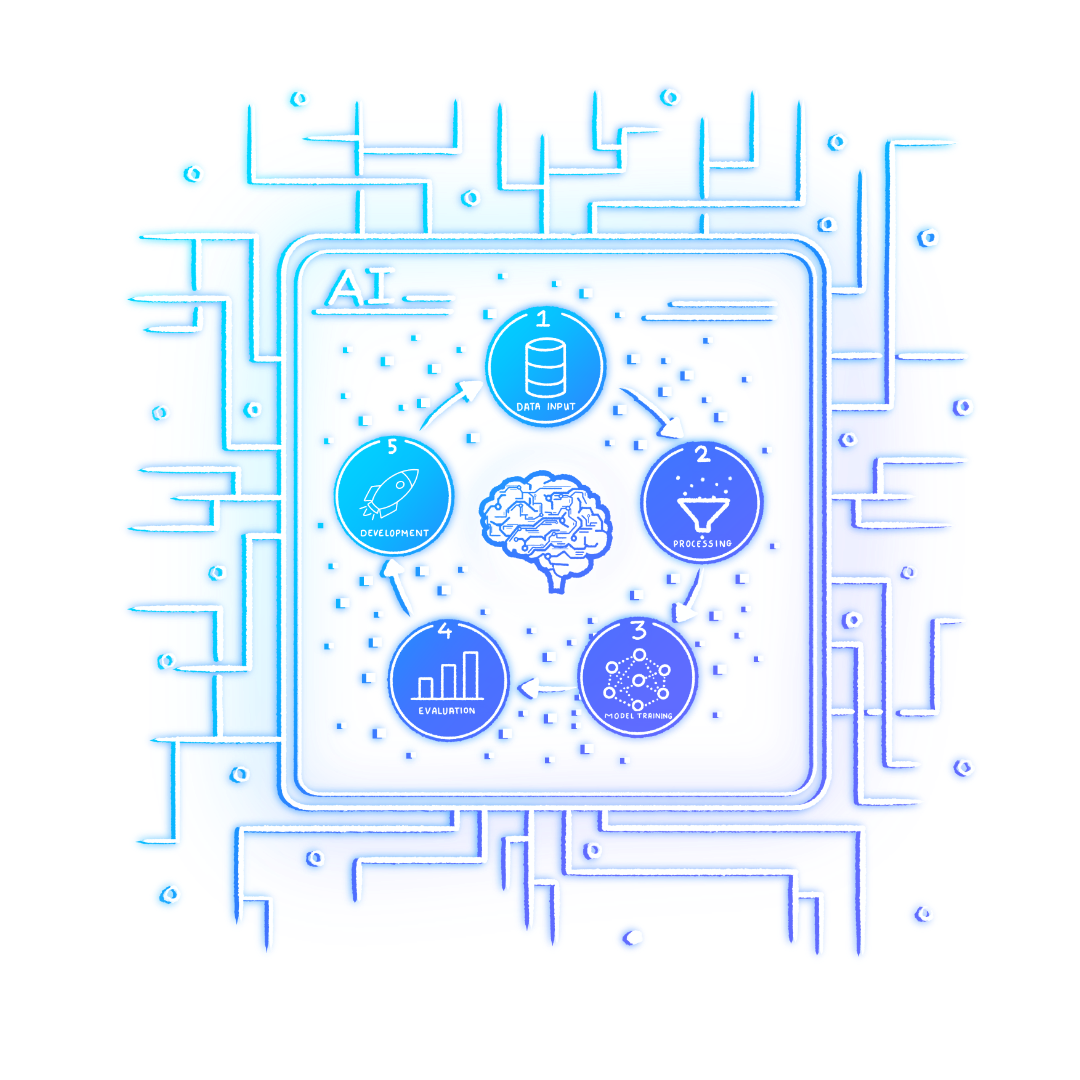
AI is changing the volume and accelerating the pace of vulnerability submissions. If you've been following our recent AI series, you already know that submission growth isn't a quality problem; it's a coordination problem. As Head of Triage, Lennaert Oudshoorn, outlines in his recent post, ‘The AI i