Reward your researchers fairly – try our bug bounty calculator today!
Intigriti
Introducing Intigriti Quick Scope
News
May 8, 2025
Setting up Burp Suite for a new bug bounty program is one of those tedious, recurring tasks every bug bounty hunter knows too well. Manually copying in-scope domains, adding out-of-scope rules, pasting mandatory request headers, and double-checking that you haven't missed an asset... all before you'
How Intigriti keeps your data safe with application-level encryption
News
March 23, 2025
Why application‑level encryption matters beyond HTTPS and basic transport‑level protections, including the specific threats it mitigates (like storage attacks and root certificate interception) for sensitive platform data. How Intigriti implements multi‑layered encryption to protect customer and r
Hybrid Pentesting: The Smart Approach to Securing your Assets
News
February 5, 2025
Pentesting-as-a-Service is your next crucial layer of security For businesses dedicated to their security, they’ll know that truly mature infrastructure doesn’t involve just one kind of protection. Vulnerability scanners, firewalls, periodic penetration tests, and bug bounties are all independent la
Power of the collective: investing in the security researcher community for shared success
Business Insights
January 30, 2025
Why investing in a strong security researcher community matters for both vulnerability discovery and organizational cyber resilience, and how engagement drives better bug bounty outcomes. How Intigriti supports and grows its global ethical hacking ecosystem through education, community events, cha
Unwavering support: Your bug bounty journey, our priority
Business Insights
January 22, 2025
How dedicated support enhances the success of your bug bounty program, from onboarding and scoping to ongoing researcher engagement and triage management. What practical resources and assistance Intigriti provides to make your bug bounty journey smoother and more effective, including consultation,
DORA is here - are you ready?
Business Insights
January 17, 2025
What the Digital Operational Resilience Act (DORA) is and why it matters for financial institutions and ICT service providers operating in the EU, including its goal to strengthen digital and cyber resilience across the sector. What the core DORA compliance requirements are, from ICT risk manageme
Innovation in action: Investing in the future of bug bounty
Business Insights
January 15, 2025
How innovation is transforming bug bounty programs by integrating new technologies, engagement models, and ecosystem support to improve vulnerability discovery and program effectiveness. What investments and practices are shaping the future of bug bounty, including advancements in tooling, platform
Supercharge your vulnerability triage: Our investment in your efficiency
Business Insights
January 9, 2025
Why effective vulnerability triage is critical to successful bug bounty programs and how substantial investment in expert triage processes can save your team time, reduce noise, and accelerate remediation. How professional triage enhances report quality and prioritisation, including expert validat
The cyber threat landscape part 5: Staying safe with multi-layered defense
Business Insights
December 5, 2024
Before diving into security controls or implementing bug bounty programs, to first establish a strong foundation in risk management and define your risk acceptance criteria. Defending your assets requires identifying and mapping each asset to the specific types and levels of threats that could impac
The cyber threat landscape part 4: Emerging technologies and their security implications
Business Insights
November 27, 2024
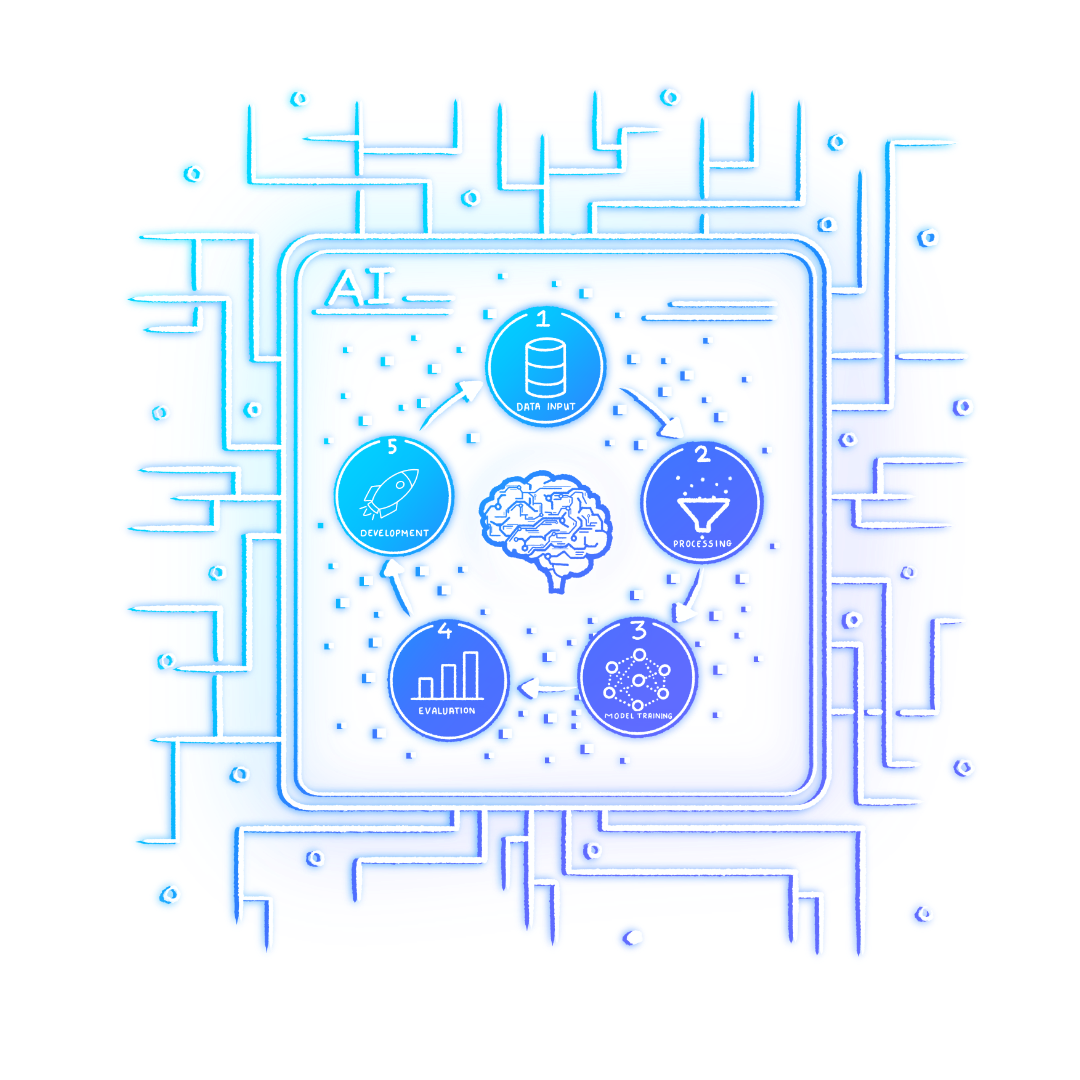
As organizations continue adopting emerging technologies, they gain immense benefits but also face new security challenges. Cloud computing, AI, IoT, and blockchain are reshaping the cyber threat landscape, introducing powerful tools for defenders along with vulnerabilities for attackers to exploit.
The cyber threat landscape part 3: Evolving attack techniques and tactics
Business Insights
November 21, 2024
As cyber attackers refine their skills, their methods evolve to exploit vulnerabilities in innovative and increasingly difficult-to-detect ways. The modern cyber threat landscape includes new attack vectors, rapid weaponization cycles, and strategic targeting, making it essential for organizations t
The cyber threat landscape part 2: Threat actors and their motivations
Business Insights
November 13, 2024
Today, the cybersecurity threat landscape is a mixed bag of attackers with different talents, interests and creativity. Threat actors span from amateur script kiddies to state-sponsored attackers, and each present their own set of challenges for organizations trying to secure their digital perimeter
The cyber threat landscape part 1: Enhancing cybersecurity strategies
Business Insights
November 6, 2024
The world continues to witness a dramatic transformation in the cybersecurity landscape. The demand for effective, global threat intelligence intensifies as geopolitical and economic shifts create a complex and uncertain world for businesses and consumers alike. As we move into 2025, most organizati
Uphold celebrates four years with Intigriti
News
October 21, 2024
Intigriti is thrilled to announce that Uphold, the leading multi-asset digital money platform, is celebrating four years of its bug bounty program with Intigriti. To mark this milestone, Intigriti sat down with Pedro Queirós, Uphold's VP of Cyber Security, to discuss the impact the bug bounty progra
Monzo launches public bug bounty program to strengthen digital security
Customer Stories
July 8, 2024
Monzo is launching its public bug bounty program, a strategic step to bolster online security. With a keen focus on user safety, this initiative aims to identify and rectify digital vulnerabilities. This move not only highlights Monzo’s dedication to security but also promises to enhance the trust a
In case you missed it on our Twitter channel, we’ve recently launched Misconfigurations Mapper (or MisconfigMapper for short)! Misconfig Mapper is a new project designed by Intigriti Hackers Team to help you find security misconfigurations in popular services used at your bug bounty/penetration test
Bug bounty ROI: Can investing in crowdsourced security help mitigate costly security breaches?
Business Insights
April 12, 2024
Factoring in whether to allocate resources for a bug bounty program in your annual cybersecurity budget can be a challenging decision. In comparison to alternative strategies, bug bounty programs offer a proactive approach to bolstering digital defenses. However, assessing the true return on investm
A hackers’ guide to online voting systems
News
March 5, 2024
In today’s digital world, online voting systems are pivotal in various domains. Businesses rely on them for award shows where the public’s vote determines winners. Music charts use online voting to influence album sales, shaping the music industry. Even self-driven communities depend on voting to ma
Navigating the PSTI Act: a guide for security professionals
Business Insights
February 13, 2024
As the implementation date of the Product Security and Telecommunications Infrastructure (PSTI) Act approaches, security professionals must understand and prepare for the regulatory changes it brings. Commencing on 29th April 2024, this legislation marks a significant milestone in product security
Exploring Bühler’s strategic collaboration with Intigriti
Customer Stories
January 22, 2024
Before collaborating with Intigriti, Bühler faced a common yet complex challenge: enhancing the effectiveness of their Vulnerability Disclosure Program (VDP). Having already been established for two years, the program was struggling under the weight of inefficiency and was largely overrun with low-q